Security / IT
Security Posture Check: Updates, Ports & Secrets
Make the routine security review continuous enough to catch drift before it becomes an incident.
Drift happens.
Security posture degrades through small changes: outdated packages, new listening services, forgotten credentials, and unreviewed exceptions.
Use OpenClaw for recurring posture review with human sign-off.
OpenClaw can run a fixed checklist, compare outputs to the last run, and hand security owners a short list of what actually changed.
Why OpenClaw Setup fits this workflow
This use case is more convincing when anchored to OpenClaw Setup’s hosted controls than when described as generic OpenClaw automation. The product already emphasizes managed environment configuration, controlled access, and persistent recurring jobs, which are exactly the ingredients a posture-review workflow needs.
OpenClaw Setup also keeps the security workflow in a stable operational environment rather than in brittle local scripts. That matters for teams that want recurring checks, preserved review instructions, and clear access boundaries without taking on the extra burden of self-hosting another privileged assistant system.
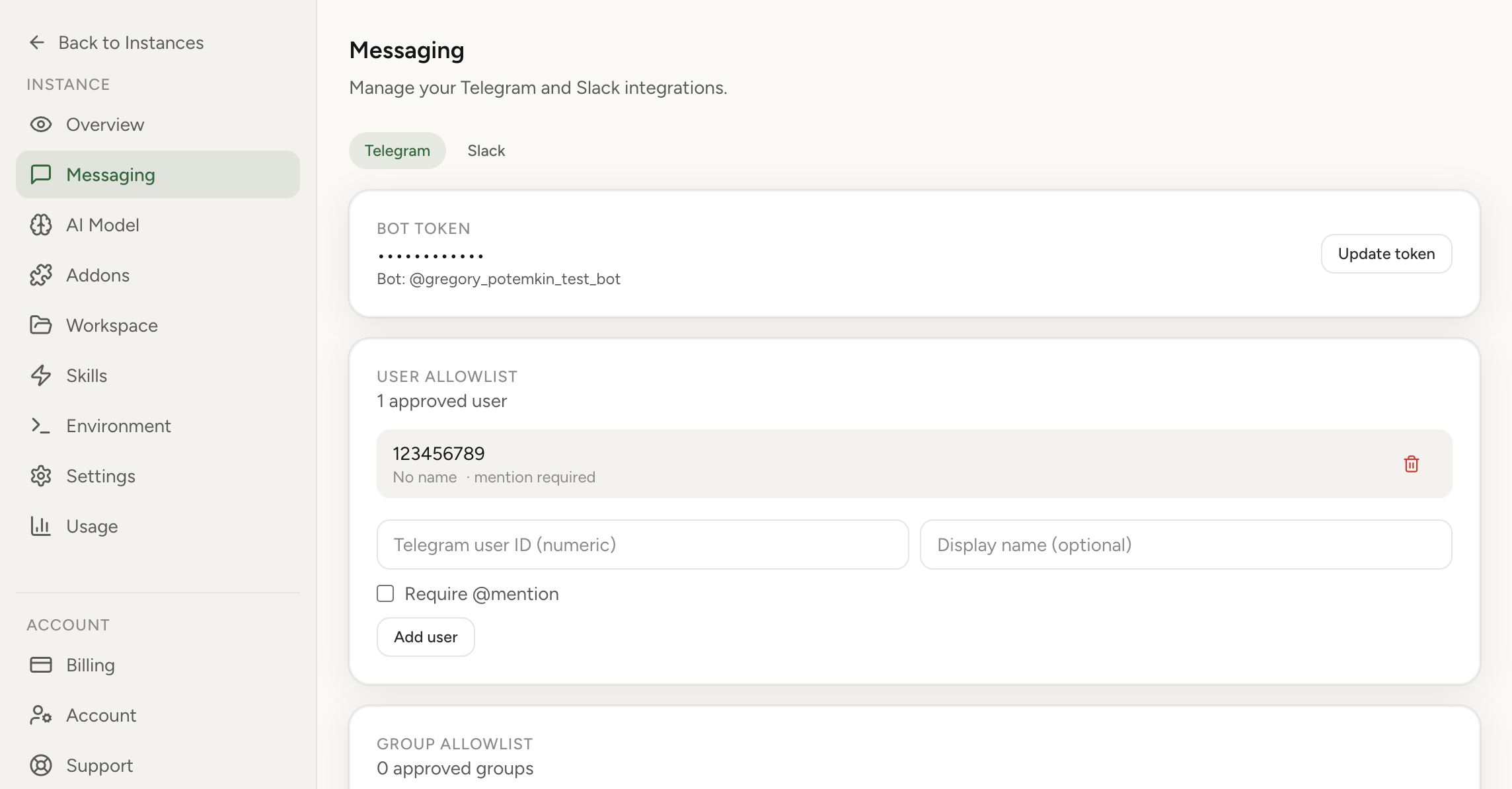
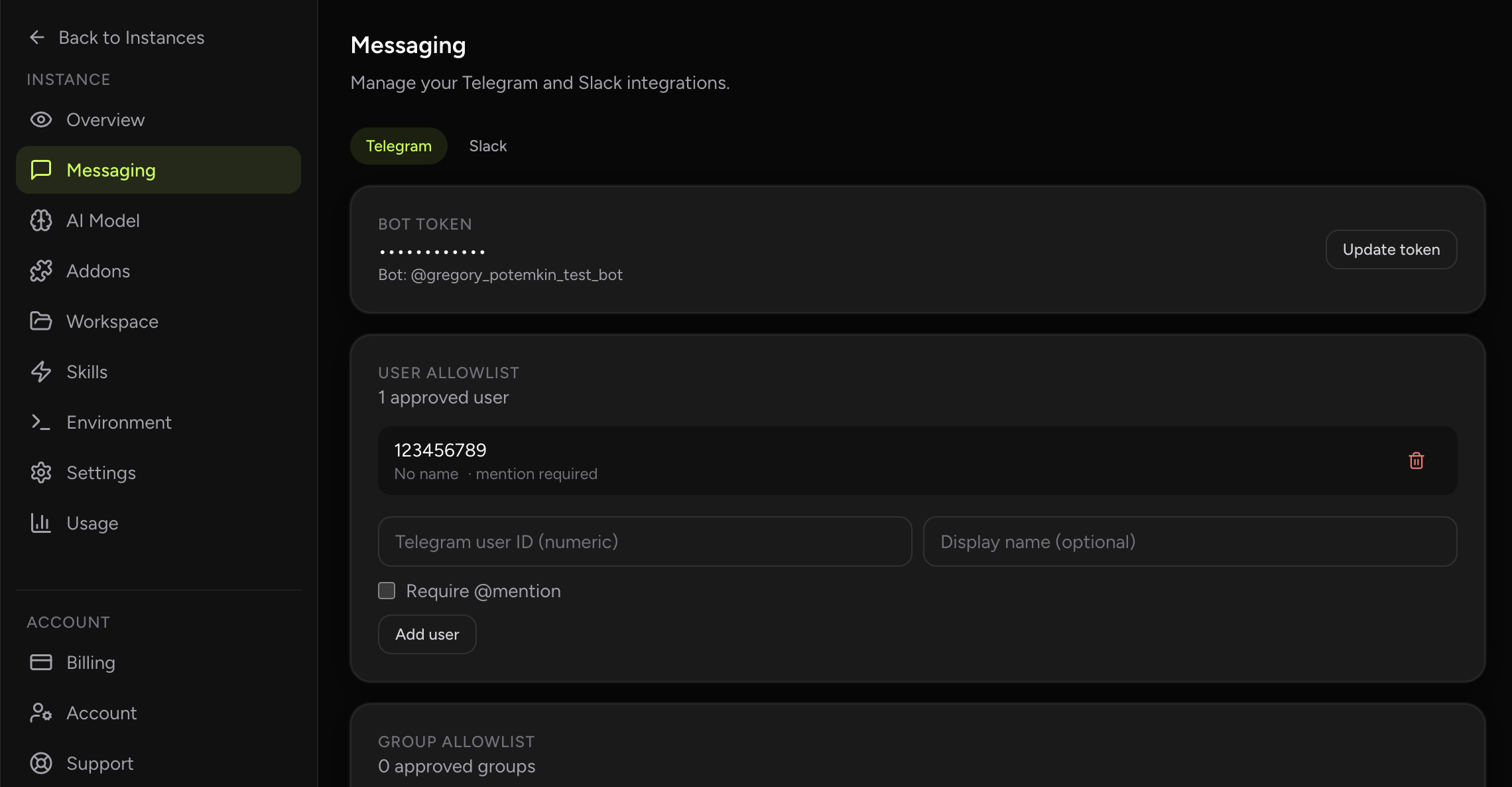
- Security allowlists reinforce the product story directly: this hosted environment is designed around explicit access control rather than wide-open experimentation.
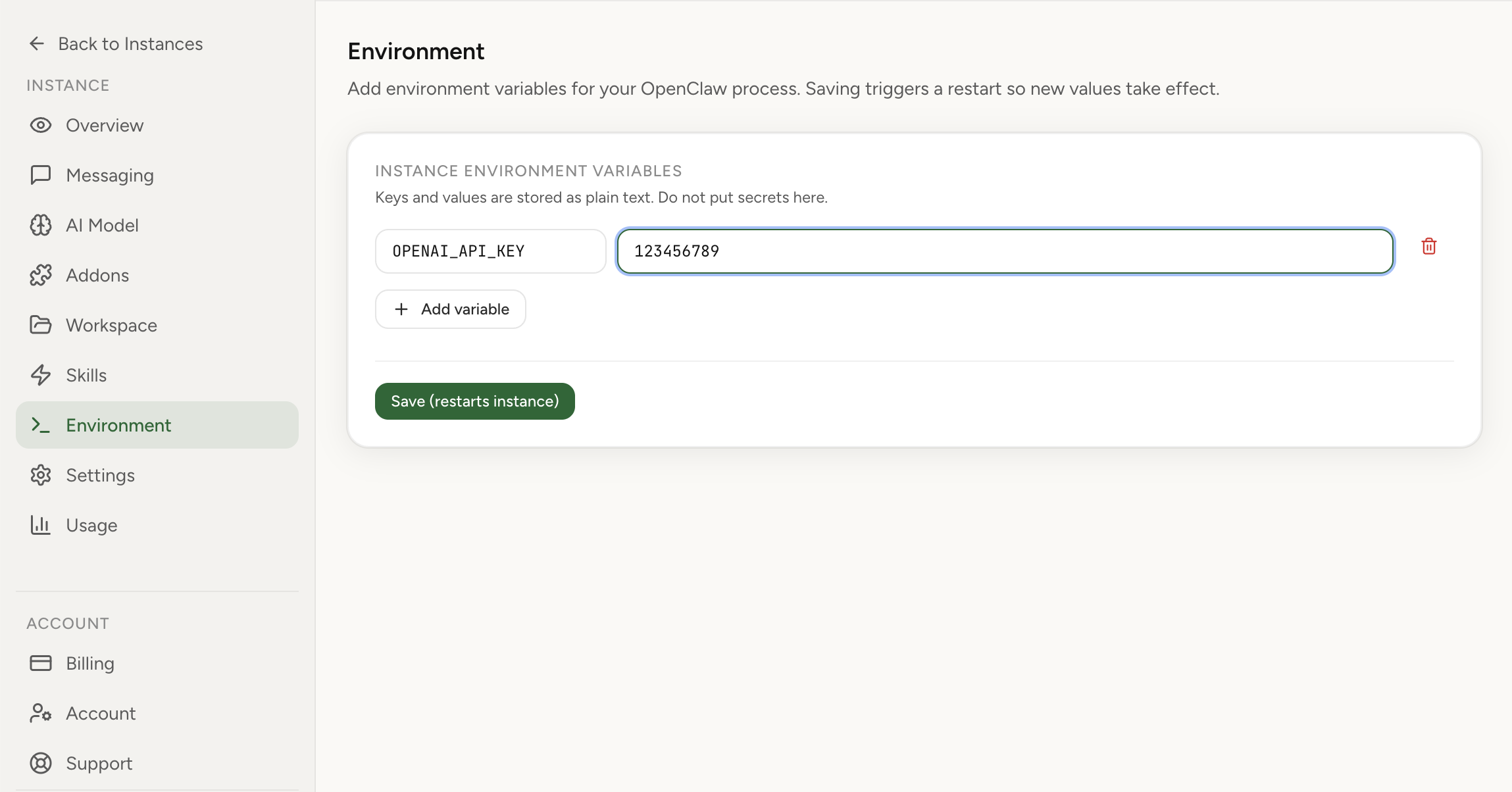
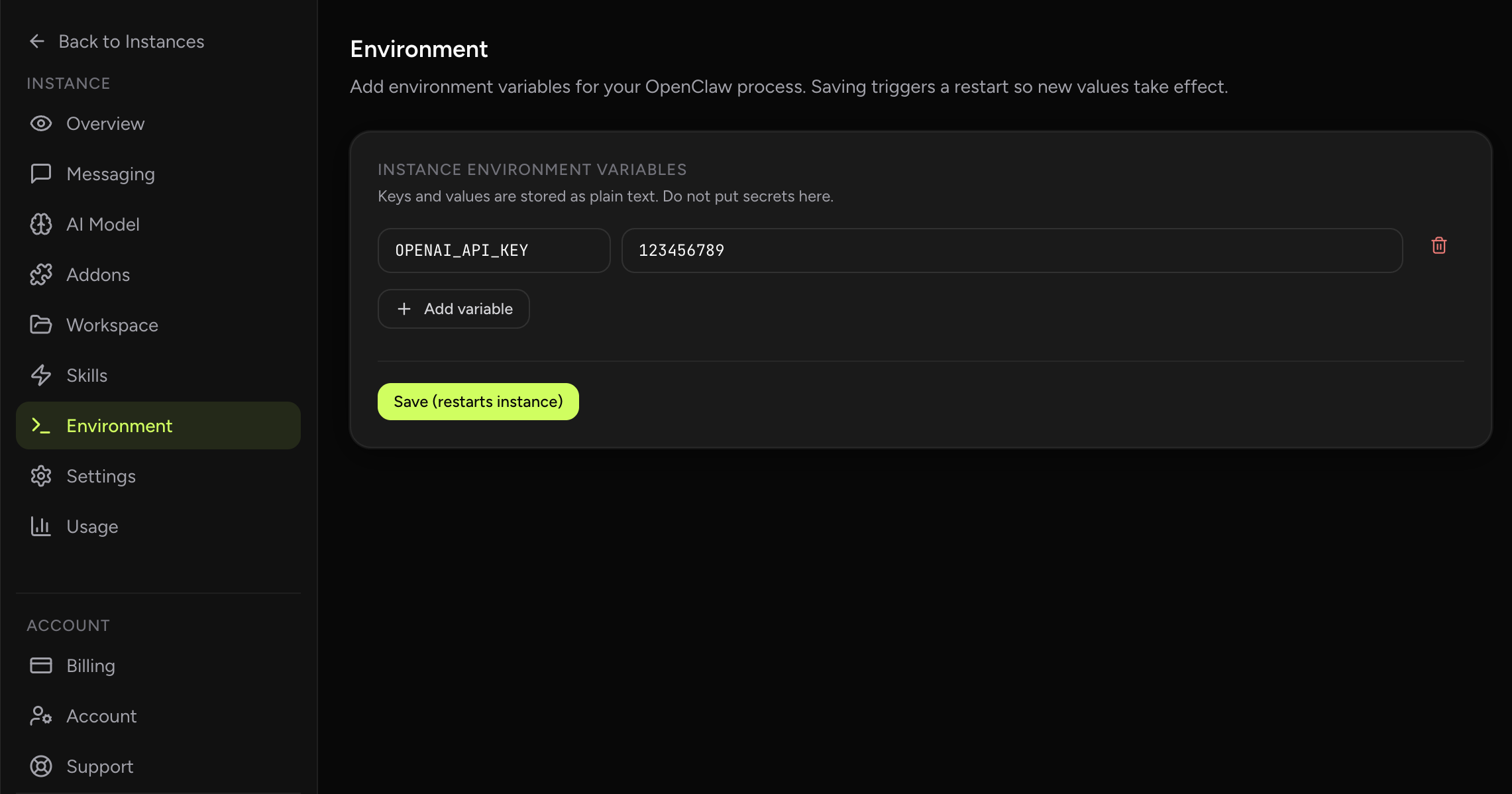
- Environment management is the natural place to keep controlled runtime variables and review the operational context of the assistant.
- Cron supports recurring posture checks, review reminders, and follow-up verification windows.
- Workspace files can store security checklists, escalation rules, and remediation standards the assistant should follow.
Why this workflow matters
Security teams do not need a quarterly PowerPoint that says patching matters. They need a recurring mechanism that turns the obvious review tasks into a living queue. That includes known exploited vulnerabilities, exposed services, credential hygiene, and configuration drift that keeps reappearing after infrastructure changes. CISA’s KEV catalog is the clearest public proof that a security checkup must be continuous. The catalog grows because exploitation keeps moving. Google and Mandiant’s response material underscores the same operational point from the other side: if posture work is neglected, incident response becomes much more expensive. A practical OpenClaw workflow sits upstream of that pain by repeatedly collecting evidence and highlighting changes.
That is why security posture check: updates, ports & secrets is a meaningful OpenClaw use case. The managed-hosting angle matters because many teams want the workflow gains of an always-on assistant without turning a side project into another system they need to harden, patch, and babysit. In practice, the assistant becomes a persistent operator for the repetitive coordination layer around the work while humans keep the authority for the consequential calls.
Real-world signals and examples
The external evidence around this workflow is already visible in the market. Known Exploited Vulnerabilities Catalog | CISA and CISA Adds Six Known Exploited Vulnerabilities to Catalog both point to the same pattern: teams are formalizing repetitive knowledge work into structured workflows that can be delegated, reviewed, and improved over time. That does not mean the role disappears. It means the role spends less time assembling context manually and more time on judgment.
CISA explicitly recommends organizations use the KEV catalog as an input to vulnerability prioritization, not as background reading. The rolling CISA alerts show why the review loop cannot be annual or purely manual; the threat set changes too often. Google’s incident-response framing reminds teams that once an incident starts, technical and communication burdens expand quickly, so prevention work has disproportionate leverage.
For a production team, that distinction matters. An OpenClaw workflow should be designed around repeatability, inspectability, and bounded scope. The assistant should gather evidence, produce a draft, or maintain a checklist faster than a human would, but the final decision point should still sit with the function owner. That is exactly what makes the workflow credible to skeptical operators.
How OpenClaw fits the workflow
The operational model is straightforward. First, OpenClaw connects to the small set of tools that already define the work: the inbox, dashboard, repository, report source, or web pages that this role checks repeatedly. Second, it runs a fixed prompt pattern on a schedule or on demand. Third, it returns structured output in a chat thread, summary note, or task-creation surface that the human already uses. Nothing about this requires a magical autonomous system. It requires disciplined workflow design.
The right prompt design for security posture check: updates, ports & secrets is evidence-first. Ask the assistant to separate observed facts from inference, missing information, and recommended next step. That single habit dramatically improves trust because the human can see what the model actually knows, what it suspects, and what still needs verification. In other words, the assistant behaves more like a good operator taking notes and less like a black box pretending to be certain.
OpenClaw is particularly well suited to this pattern because it can blend scheduled jobs, tool use, messaging, and human review into one thread. Instead of running a point solution for summarization and another tool for reminders and another for browser work, the team gets one place where the workflow can live end to end. That reduces coordination overhead, which is often the real tax on the role.
High-leverage automation patterns
The most useful automation patterns for security posture check: updates, ports & secrets are the ones that remove queue work and repeated context assembly. They give the role a cleaner first pass at the problem and make the human step more focused. In practice, that often means one or two scheduled routines, a handful of on-demand prompts, and a very explicit handoff point when ambiguity or risk rises.
- Patch and KEV review: compare installed software and exposed services against the current vulnerability queue and known high-priority items.
- Exposure snapshot: list listening ports, unexpected processes, changed network paths, or stale secrets to review with an owner.
- Drift comparison: produce a week-over-week diff so the team sees what changed rather than re-reading the same baseline every time.
- Remediation queueing: turn findings into tickets with severity, owner, and due date instead of leaving them as narrative notes.
Rollout plan for a real team
A staff-level rollout starts smaller than most teams expect. You do not begin by automating the highest-stakes decision in the process. You begin by automating the most repetitive preparation step. Once the team trusts the assistant’s retrieval, formatting, and summarization quality, you expand to higher-leverage steps such as draft creation, queue management, or suggested next actions. That sequencing protects trust while still delivering value early.
The change-management side matters too. Someone should own the prompt, the review criteria, and the weekly feedback loop. The fastest way to kill adoption is to drop an assistant into the workflow and never tighten it again. The best teams treat the assistant like a process asset: they measure output quality, trim noisy steps, add missing context, and gradually turn a generic workflow into one that feels native to the team.
- Start with visibility and diffs; do not let the assistant make security changes automatically at the beginning.
- Map the checklist to your environment so results are comparable across runs and hosts.
- Tag each finding as observed evidence, inferred risk, or recommended action to prevent overstatement.
- Build the review into a weekly or twice-weekly cadence so it becomes normal operational work.
Example prompts to start with
A good starting prompt set should be narrow, repetitive, and easy to judge. The goal is not creative novelty. The goal is a repeatable operating motion where the assistant produces something the human can accept, correct, or reject quickly. The sample prompts below work best when paired with your own team-specific instructions, naming conventions, and output format.
- "Weekly: check updates and critical CVEs"
- "List listening ports and suspicious services"
- "Report diff vs last week"
How to measure success
Success for this use case should be measured in operating outcomes, not novelty. If the assistant is helpful, cycle time should drop, the quality of handoffs should improve, and humans should spend less time on clerical reconstruction of context. If those outcomes do not move, the workflow probably is not integrated deeply enough yet or it is automating the wrong step.
This is also where many teams discover whether the workflow is actually sticky. A strong OpenClaw use case keeps getting used because it becomes part of the team’s routine cadence. A weak one gets demoed once and forgotten. The metrics below are meant to catch that difference early.
It is worth reviewing these metrics with examples, not just numbers. Look at one week where the assistant clearly helped and one week where it clearly created rework. That comparison usually exposes whether the underlying issue is prompt quality, missing tool access, weak review discipline, or simply a bad workflow choice. Teams that keep tuning from real examples tend to compound value; teams that only watch dashboards often miss the practical reasons adoption rises or stalls.
- Time to identify newly relevant KEV items
- Number of posture changes surfaced per checkup
- Mean time to remediation for routine findings
- Reduction in repeated configuration drift
What a mature setup looks like
A mature security posture check: updates, ports & secrets workflow does not live as an isolated demo prompt. It becomes part of the team’s normal weekly rhythm. There is a named owner, a clear destination for outputs, a review habit for bad suggestions, and a stable connection to the systems that hold the source data. Once that happens, the assistant stops feeling like an experiment and starts feeling like operational infrastructure. That transition is usually when teams notice the real gain: not just faster task completion, but less managerial drag around reminding, summarizing, and chasing the same work every week.
This is also where managed hosting changes the economics. If the assistant needs to be available on schedule, hold credentials securely, and run the same workflow repeatedly, the team benefits from an environment that is already set up for continuity. OpenClaw works best when the workflow is specific, the boundaries are explicit, and the outputs land where the team already works. In that setting, the assistant is not replacing the profession. It is removing the repetitive coordination tax that keeps the profession from spending enough time on its highest-value judgment.
Guardrails and common mistakes
The main design principle is bounded autonomy. Let the assistant gather, summarize, compare, and draft aggressively. Keep final authority with the human where money, security, compliance, customer commitments, or irreversible operational changes are involved. That split is not a compromise; it is usually the most efficient design. Humans should review only the parts where review creates real value.
Most failures in agent rollouts come from one of two extremes: either the team keeps the assistant so constrained that it saves no time, or it removes safeguards too early and loses trust after one bad output. The practical middle path is to give the assistant a lot of preparation work, visible logs, and explicit escalation boundaries. That makes the system useful without making it reckless.
- Running a checklist without preserving previous-state comparison
- Treating every finding as equal severity and overwhelming owners
- Allowing automated remediation before the team trusts the detection quality
- Keeping findings in chat without creating an accountable remediation queue
Suggested OpenClaw tools
This workflow usually combines the following tool surfaces inside one managed thread: exec, cron, message.
Sources and further reading
- Known Exploited Vulnerabilities Catalog | CISA CISA maintains the authoritative list of vulnerabilities known to be exploited in the wild and recommends prioritizing them in remediation programs.
- CISA Adds Six Known Exploited Vulnerabilities to Catalog CISA’s rolling alerts show why a security checkup needs a living queue instead of a static annual audit.
- Cyber Incident Response Service | Google Cloud Google highlights the value of 24/7 response coverage, threat intelligence, and coordinated technical plus crisis management.